Information Security
We Advance IT Security
The Information Security research group of the InIT addresses issues related to the development of secure software systems (Software Security) and the study of cyber attacks and defense (Cyber Attacks and Defense). Among other things, we address questions such as:
- How can functionality be implemented in a secure manner?
- How can the level of automation in security testing be increased?
- How can publicly available information be used to detect threats?
- What security mechanisms are needed for future communication networks?
- What is the role of security awareness and how can it be improved?
The knowledge gained from applied research and development is also incorporated into our continuing education Offerings:
and our Bachelor- (Introduction to Computer and Communication Security, IT Security, Software and System Security 1, Software and System Security 2) and Master modules (IT-Security).
The Information Security research group is part of the ZHAW Cybersecurity Community. As such, it is also a member of the Swiss Support Center for Cybersecurity (sscc).
Software Security
The topic of Software Security covers the modeling, realization, and analysis of software systems that fulfill a number of security requirements.
Our research concentrates on the analysis by means of (automated) security testing and the development of novel security mechanisms and protocols. Thereby, the quality, efficiency and reproducibility of the tests as well as the protection of domain-specific functionality are the main focus.
A current project on this topic:
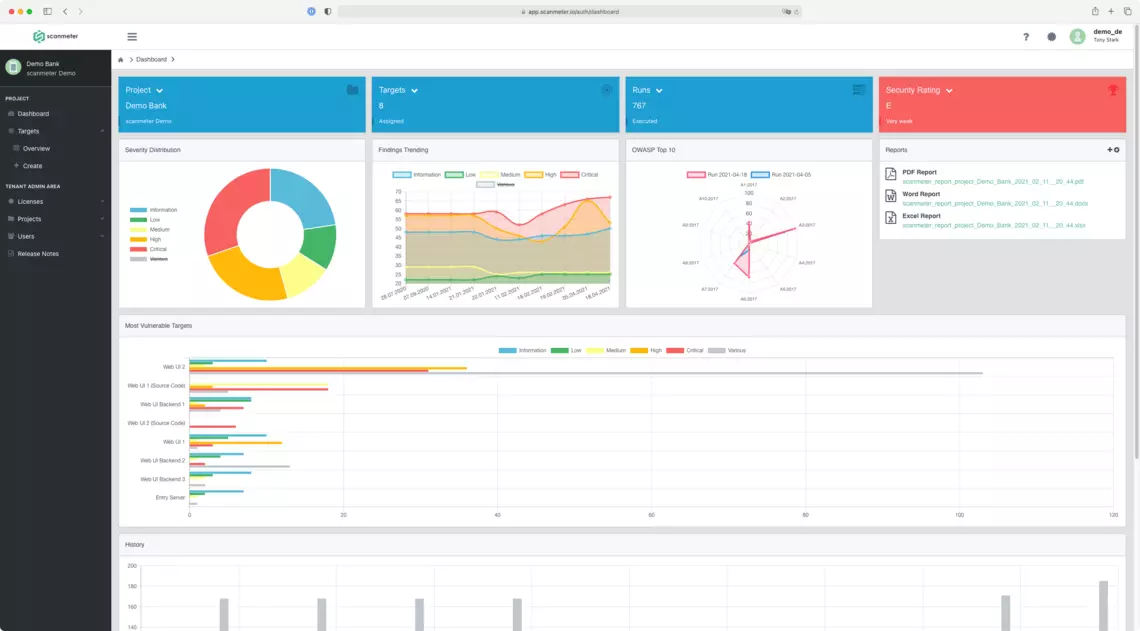
In this R&D project, scanmeter - a service for the automated security analysis of IT systems - is being extended by three innovative components. This will significantly increase the level of automation and test coverage, significantly improve customer benefits, and expand the fields of applications. Specifically, the following should be achieved in the project: (1) scanmeter will support automated security testing of APIs, significantly increasing the range of applications (e.g., to modern web applications, mobile apps and Internet of Things (IoT) devices); (2) scanmeter will be able to detect all types of access control vulnerabilities in web applications, providing comprehensive support for this critical vulnerability type; and (3) scanmeter will support arbitrary authentication processes in web applications and APIs, enabling full test automation with respect to authentication as well.
The project is carried out in cooperation between InIT and scanmeter GmbH.
Cyber Attacks and Defense
The topic Cyber Attack and Defense covers the modeling, analysis, and realization of cyber attacks and of defensive measures.
We research and develop solutions to combat current threats more effectively. In particular, we focus on threats related to the introduction and use of new technologies (e.g. 5G/6G networks), the improvement of the defense posture (e.g. using OSINT), machine learning and the human factor.
A current project on this topic:
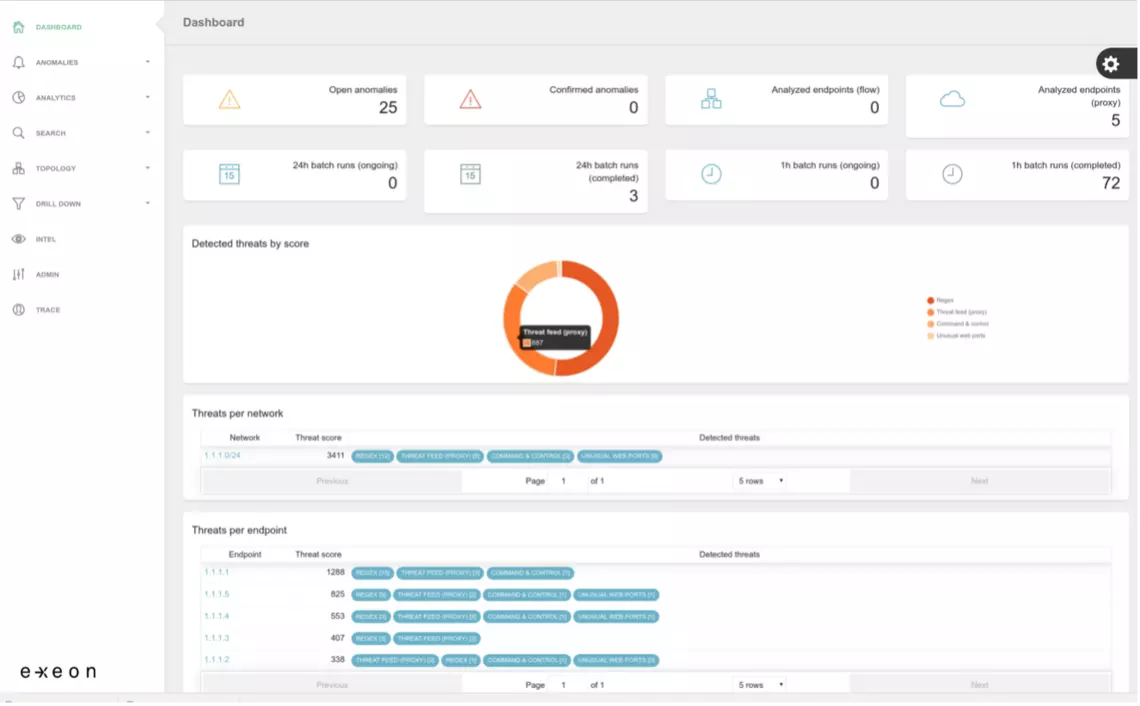
This project extends Exeon Analytics' ExeonTrace product with HostDetective Next Generation (HD.ng), a tool to identify and mitigate Web-related data breaches. HD.ng implements a novel active and passive Web server assessment method to determine the type, purpose and risk score of a Web server. This project builds on the results of the HostDetective project.
Continuing Education
Our CAS Applied IT Security (German only) offers the opportunity to computer scientists, practitioners and career changers the opportunity to build and enhance their foundation in IT Security, one of the most important growth markets in IT. Participants will be introducted into security architecture and management, cryptology and network security as well as software and systems security. They will be given the opportunity to apply their new skills in extensive and practice oriented labs.
-
Dynamic Analysis of Internal Android Systems
In this project, we focus on the current state of Android security. One main focus will be to determine current difficulties and limitations that hinder security researchers in performing a dynamic analysis of Android pre-installed software components such as pre-installed apps or native libraries. In a first step, ...
-
Automated Information Security Governance and Risk Management
-
CYREN ZH: Cyber Resilience Network For The Canton Of Zurich
How can we better protect ourselves from cyber threats? The answer to this question is as complex as cyber security itself, because the right balance must always be found between technical possibilities and political, social and economic interests. The increasing digitalisation of critical infrastructures in ...
-
Gür, Gürkan; Porambage, Pawani; Osorio, Diana Moya; Yavuz, Attila A.; Liyanage, Madhusanka,
2024.
6G security vision : a concise update [paper].
In:
2023 IEEE Future Networks World Forum (FNWF).
IEEE Future Networks World Forum, Baltimore, USA, 13-15 November 2023.
IEEE.
Available from: https://doi.org/10.1109/FNWF58287.2023.10520627
-
Deniz, Eren; Cantali, Gokcan; Ozay, Ozcan; Yildirim, Onur; Gür, Gürkan; Alagoz, Fatih,
2024.
Towards data analytics based PIM detection in wireless networks [paper].
In:
2023 IEEE 28th International Workshop on Computer Aided Modeling and Design of Communication Links and Networks (CAMAD).
28th International Workshop on Computer Aided Modeling and Design of Communication Links and Networks (CAMAD), Edinburgh, United Kingdom, 6-8 November 2023.
IEEE.
pp. 1-6.
Available from: https://doi.org/10.1109/CAMAD59638.2023.10478405
-
Sutter, Thomas; Kehrer, Timo; Rennhard, Marc; Tellenbach, Bernhard; Klein, Jacques,
2024.
Dynamic security analysis on Android : a systematic literature review.
IEEE Access.
12, pp. 57261-57287.
Available from: https://doi.org/10.1109/ACCESS.2024.3390612
-
Kalla, Anshuman; de Alwis, Chamitha; Gochhayat, Sarada Prasad; Gür, Gürkan; Liyanage, Madhusanka; Porambage, Pawani,
2024.
Emerging directions for blockchainized 6G.
IEEE Consumer Electronics Magazine.
13(2), pp. 42-51.
Available from: https://doi.org/10.1109/MCE.2022.3164530
-
Rüedlinger, Andreas; Klauser, Rebecca; Lamprakis, Pavlos; Happe, Markus; Tellenbach, Bernhard; Veyisoglu, Onur; Trammell, Ariane,
2024.
FeedMeter : evaluating the quality of community-driven threat intelligence [paper].
In:
Proceedings of the 10th International Conference on Information Systems Security and Privacy - ICISSP.
10th International Conference on Information Systems Security and Privacy (ICISSP), Rome, Italy, 26-28 February 2024.
SciTePress.
pp. 54-66.
Available from: https://doi.org/10.5220/0012357600003648